Merge pull request #417 from AnonymousWP/416-Feat]-Separate-Docker-Compose-files
Add separate Docker Compose files
This commit is contained in:
141
README.md
141
README.md
@@ -9,36 +9,45 @@
|
||||
|
||||
[[Website](https://sn1persecurity.com/wordpress/)] [[Blog](https://sn1persecurity.com/wordpress/blog/)] [[Shop](https://sn1persecurity.com/wordpress/shop)] [[Documentation](https://sn1persecurity.com/wordpress/documentation/)] [[Demo](https://www.youtube.com/c/Sn1perSecurity/videos)] [[Find Out More](https://sn1persecurity.com/wordpress/external-attack-surface-management-with-sn1per/)]
|
||||
|
||||
|
||||
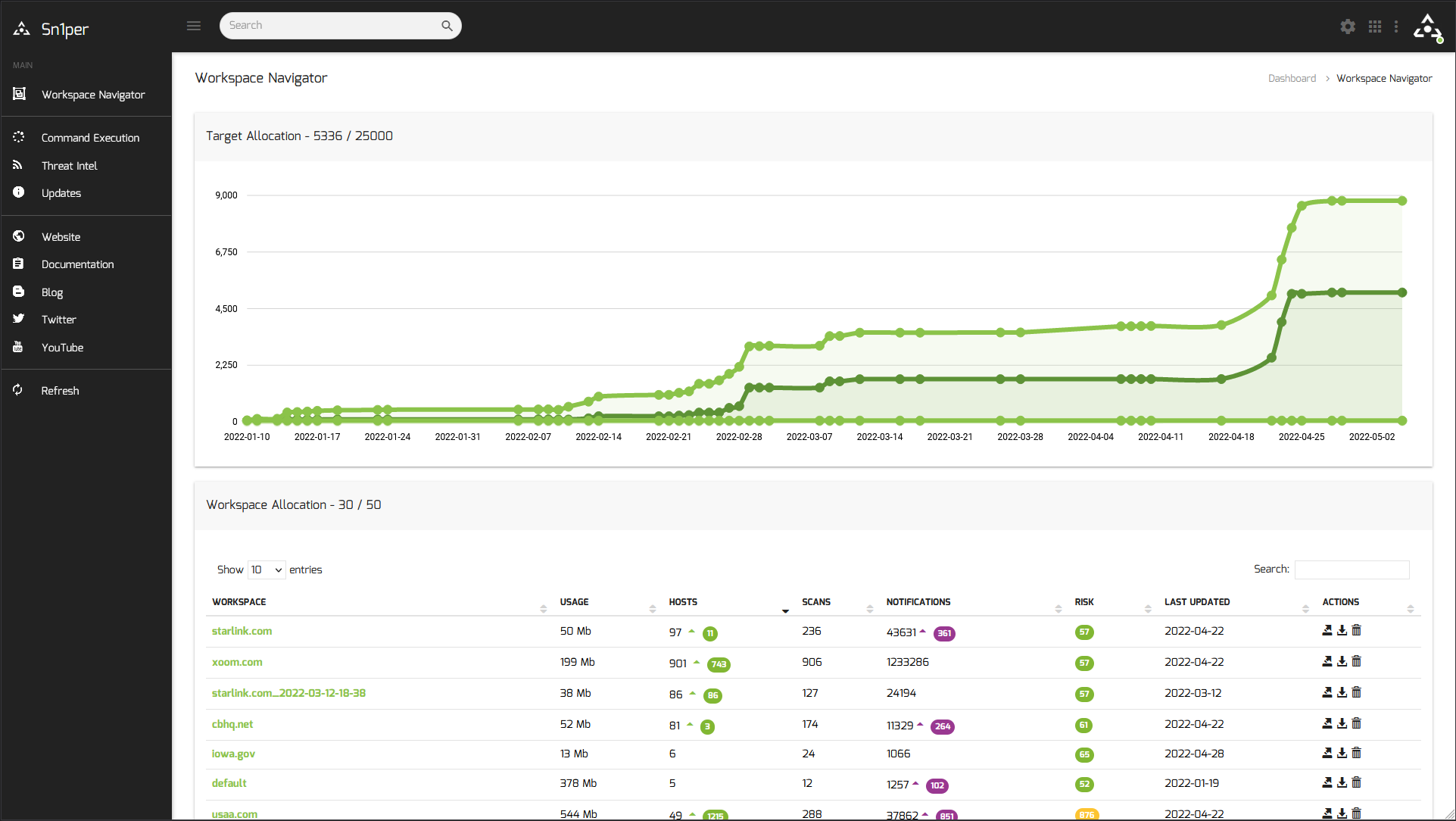
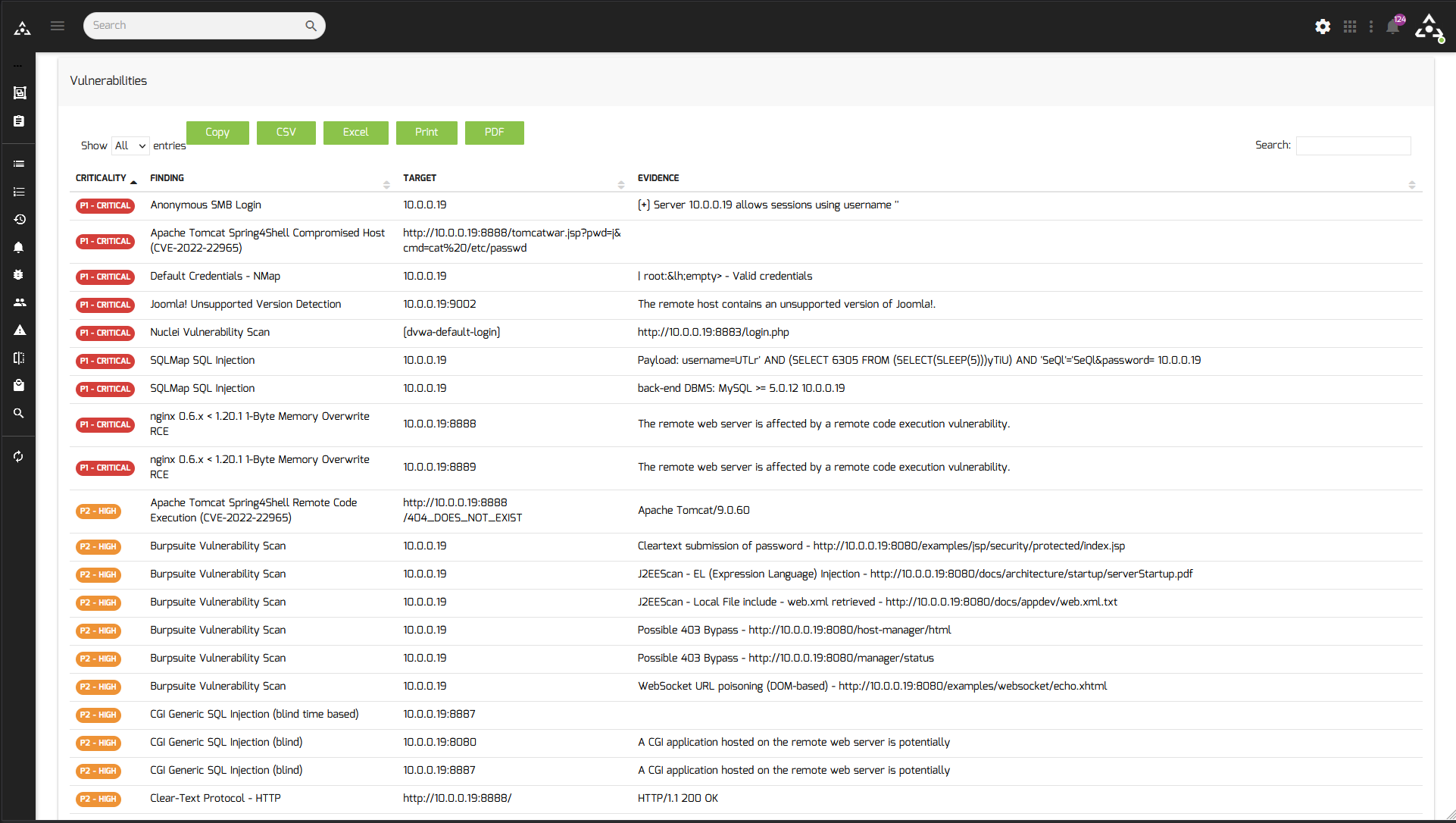
## Attack Surface Management Platform
|
||||
|
||||
### Discover hidden assets and vulnerabilities in your environment
|
||||
|
||||
#### [[Find out more](https://sn1persecurity.com/wordpress/shop)]
|
||||
|
||||
[](https://sn1persecurity.com/)
|
||||
|
||||
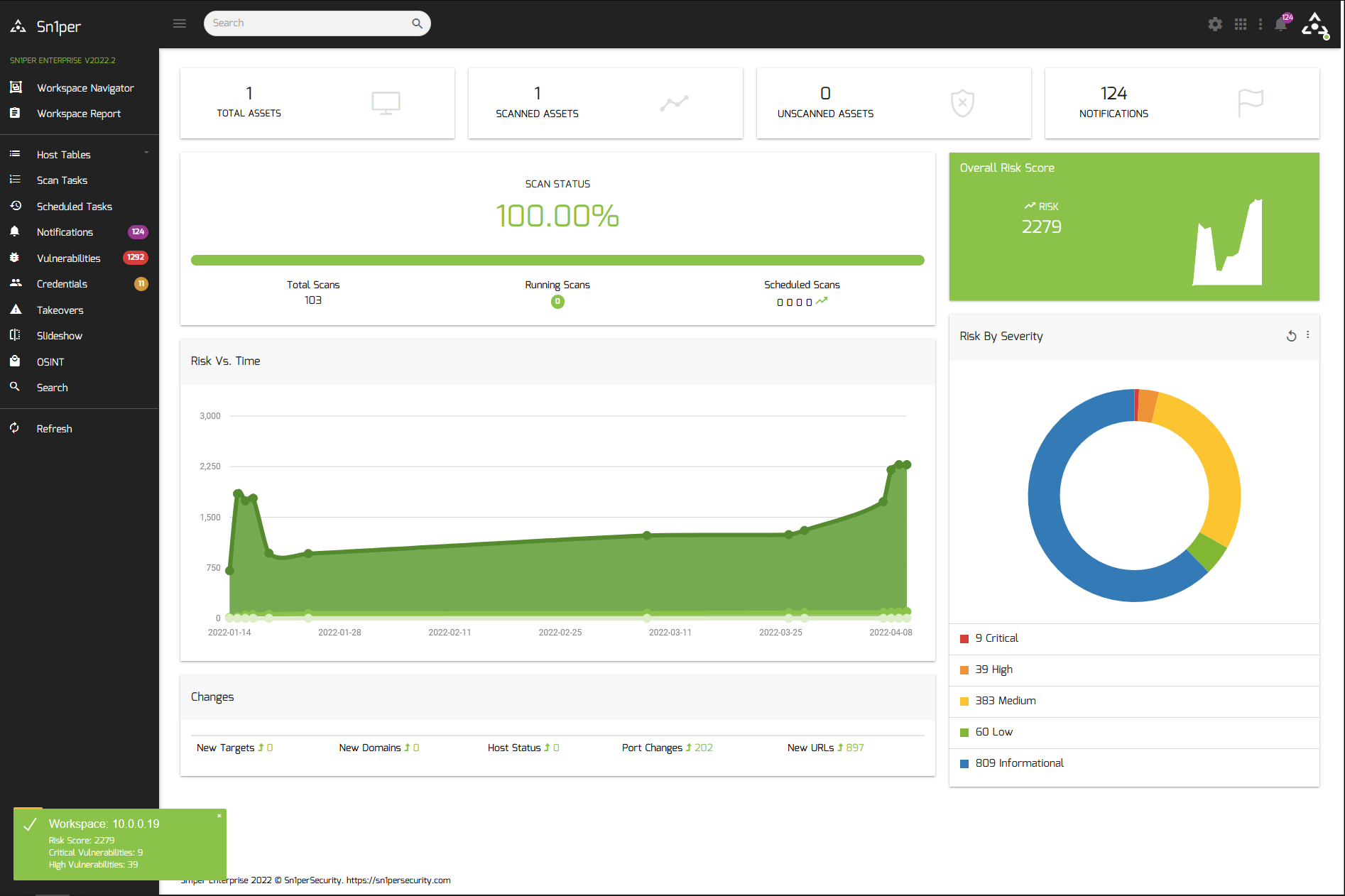
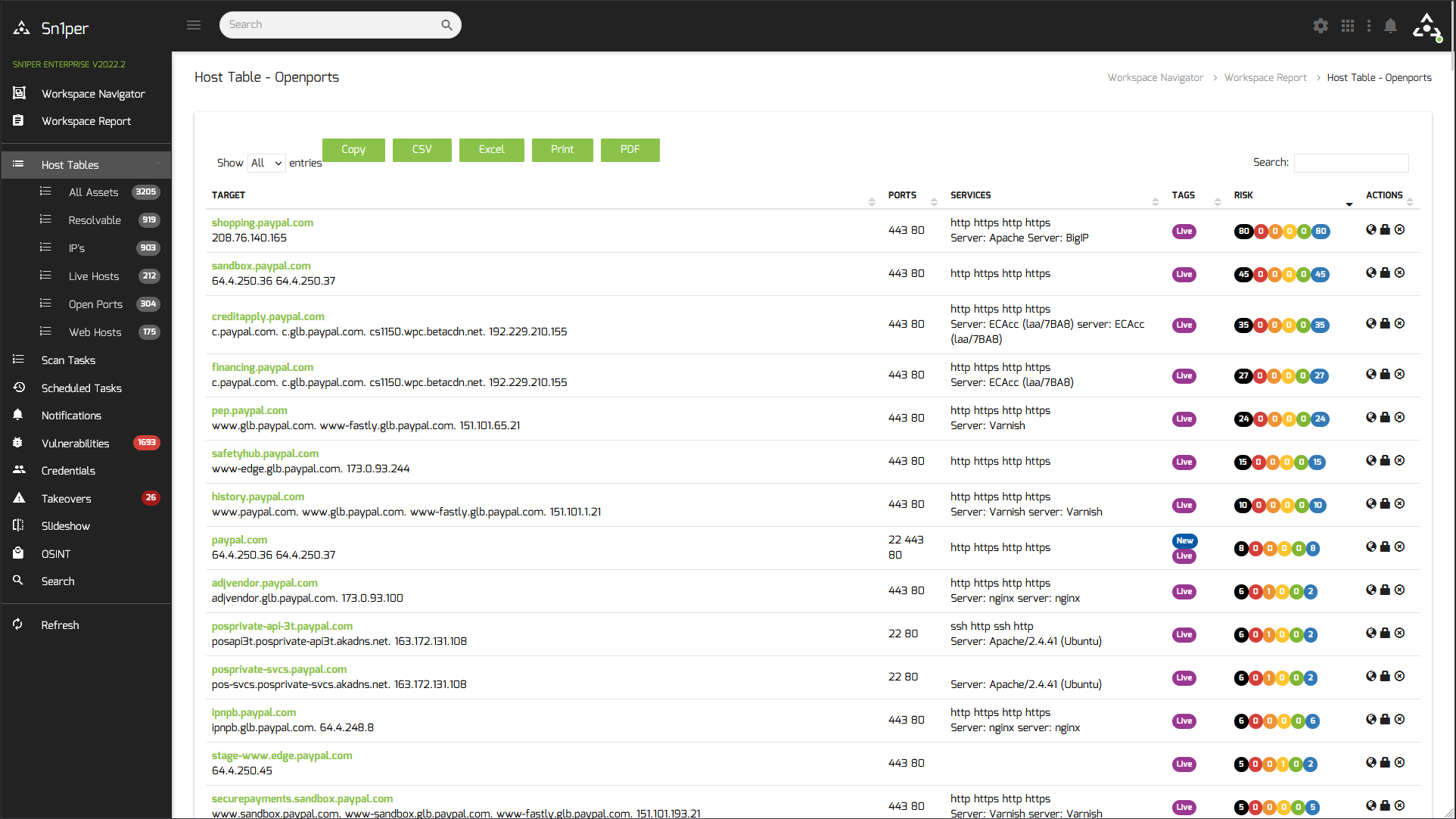
## The ultimate pentesting toolkit.
|
||||
Integrate with the leading commercial and open source vulnerability scanners to scan for the latest CVEs and vulnerabilities.
|
||||
## The ultimate pentesting toolkit
|
||||
|
||||
Integrate with the leading commercial and open source vulnerability scanners to scan for the latest CVEs and vulnerabilities.
|
||||
|
||||
[](https://sn1persecurity.com/)
|
||||
|
||||
### Automate the most powerful tools.
|
||||
### Automate the most powerful tools
|
||||
|
||||
Security tools are expensive and time-consuming, but with Sn1per, you can save time by automating the execution of these open source and commercial tools to discover vulnerabilities across your entire attack surface.
|
||||
|
||||
[](https://sn1persecurity.com/)
|
||||
|
||||
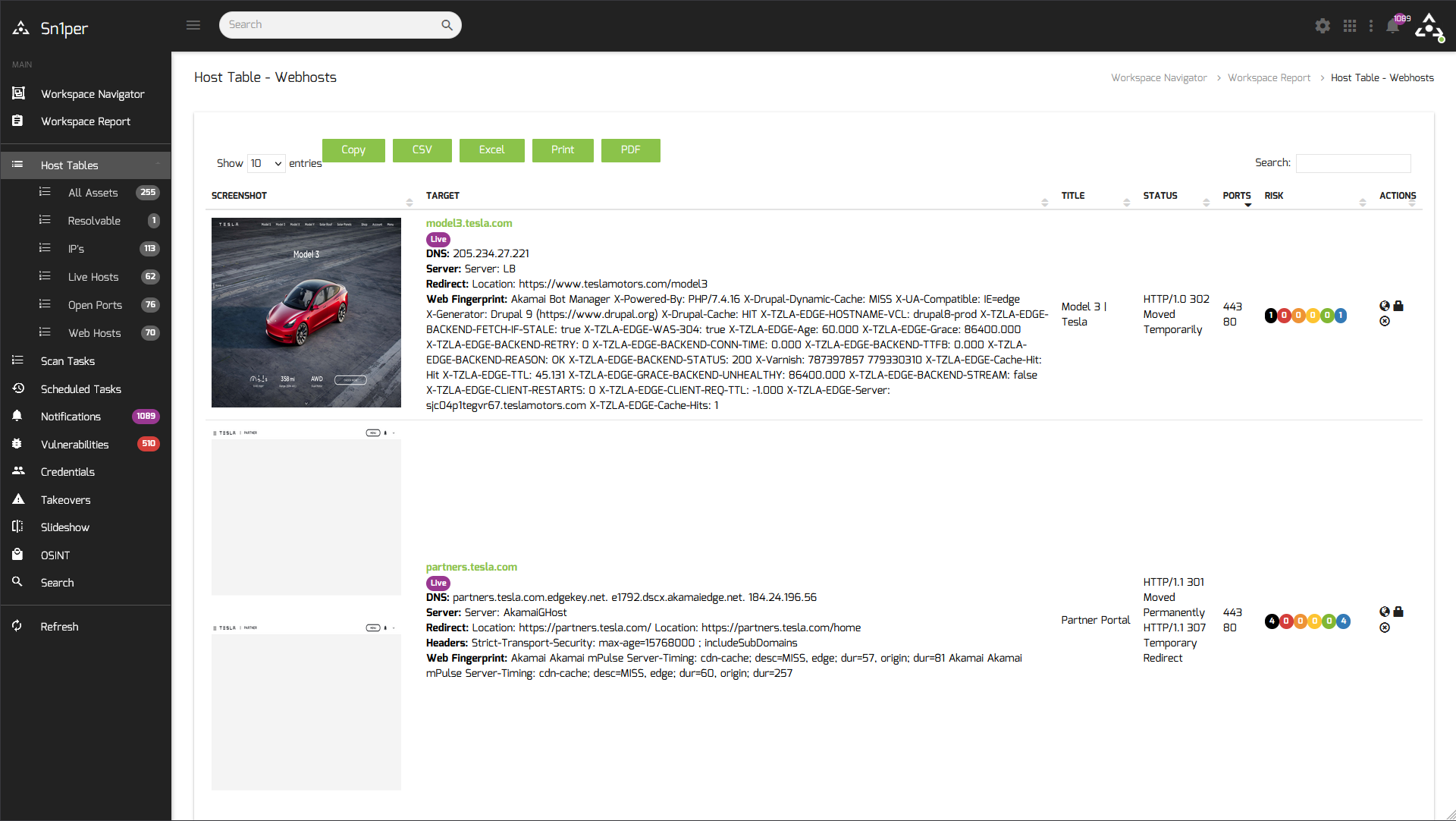
### Find what you can't see.
|
||||
Hacking is a problem that's only getting worse. But, with Sn1per, you can find what you can’t see—hidden assets and vulnerabilities in your environment.
|
||||
### Find what you can't see
|
||||
|
||||
Hacking is a problem that's only getting worse. But, with Sn1per, you can find what you can’t see—hidden assets and vulnerabilities in your environment.
|
||||
|
||||
[](https://sn1persecurity.com/)
|
||||
|
||||
### Discover and prioritize risks in your organization.
|
||||
### Discover and prioritize risks in your organization
|
||||
|
||||
Sn1per is a next-generation information gathering tool that provides automated, deep, and continuous security for organizations of all sizes.
|
||||
|
||||
[](https://sn1persecurity.com/)
|
||||
|
||||
### See Sn1per in action!
|
||||
### See Sn1per in action
|
||||
|
||||
[](https://www.youtube.com/c/Sn1perSecurity/videos)
|
||||
|
||||
### News
|
||||
|
||||
- #### [Automated Penetration Testing Guide - Your Ultimate Resource](https://sn1persecurity.com/wordpress/penetration-testing-guide/)
|
||||
- #### [Sn1per Enterprise v20230516 Released!](https://sn1persecurity.com/wordpress/sn1per-enterprise-v20230516-released/)
|
||||
- #### [Dark Web Monitoring: Securing Your External Attack Surface](https://sn1persecurity.com/wordpress/dark-web-monitoring-securing-your-external-attack-surface/)
|
||||
@@ -52,6 +61,7 @@ Sn1per is a next-generation information gathering tool that provides automated,
|
||||
- #### [Sn1per Professional v10.0 Released!](https://sn1persecurity.com/wordpress/sn1per-professional-v10-released/)
|
||||
|
||||
## Kali/Ubuntu/Debian/Parrot Linux Install
|
||||
|
||||
```
|
||||
git clone https://github.com/1N3/Sn1per
|
||||
cd Sn1per
|
||||
@@ -59,31 +69,50 @@ bash install.sh
|
||||
```
|
||||
|
||||
## AWS AMI (Free Tier) VPS Install
|
||||
|
||||
[](https://aws.amazon.com/marketplace/pp/prodview-rmloab6wnymno)
|
||||
|
||||
To install Sn1per using an AWS EC2 instance:
|
||||
|
||||
1. Go to https://aws.amazon.com/marketplace/pp/prodview-rmloab6wnymno and click the “Continue to Subscribe” button
|
||||
1. Go to <https://aws.amazon.com/marketplace/pp/prodview-rmloab6wnymno> and click the “Continue to Subscribe” button
|
||||
2. Click the “Continue to Configuration” button
|
||||
3. Click the “Continue to Launch” button
|
||||
4. Login via SSH using the public IP of the new EC2 instance
|
||||
|
||||
## Docker Install
|
||||
|
||||
[](https://hub.docker.com/r/sn1persecurity/sn1per)
|
||||
|
||||
From a new Docker console, run the following commands.
|
||||
```
|
||||
Download https://raw.githubusercontent.com/1N3/Sn1per/master/Dockerfile
|
||||
docker build -t sn1per .
|
||||
docker run -it sn1per /bin/bash
|
||||
### Kali Linux-based Sn1per
|
||||
|
||||
or
|
||||
1. Run the Docker Compose file
|
||||
|
||||
docker pull xer0dayz/sn1per
|
||||
docker run -it xer0dayz/sn1per /bin/bash
|
||||
```
|
||||
```bash
|
||||
sudo docker compose up
|
||||
```
|
||||
|
||||
1. Run the container
|
||||
|
||||
```bash
|
||||
sudo docker run -it sn1per-kali-linux /bin/bash
|
||||
```
|
||||
|
||||
### BlackArch-based Sn1per
|
||||
|
||||
1. Run the Docker Compose file
|
||||
|
||||
```bash
|
||||
sudo docker compose -f docker-compose-blackarch.yml up
|
||||
```
|
||||
|
||||
1. Run the container
|
||||
|
||||
```bash
|
||||
sudo docker run -it sn1per-blackarch /bin/bash
|
||||
```
|
||||
|
||||
## Usage
|
||||
|
||||
```
|
||||
[*] NORMAL MODE
|
||||
sniper -t <TARGET>
|
||||
@@ -174,49 +203,55 @@ sniper -u|--update
|
||||
```
|
||||
|
||||
## Modes
|
||||
* **NORMAL:** Performs basic scan of targets and open ports using both active and passive checks for optimal performance.
|
||||
* **STEALTH:** Quickly enumerate single targets using mostly non-intrusive scans to avoid WAF/IPS blocking.
|
||||
* **FLYOVER:** Fast multi-threaded high level scans of multiple targets (useful for collecting high level data on many hosts quickly).
|
||||
* **AIRSTRIKE:** Quickly enumerates open ports/services on multiple hosts and performs basic fingerprinting. To use, specify the full location of the file which contains all hosts, IPs that need to be scanned and run ./sn1per /full/path/to/targets.txt airstrike to begin scanning.
|
||||
* **NUKE:** Launch full audit of multiple hosts specified in text file of choice. Usage example: ./sniper /pentest/loot/targets.txt nuke.
|
||||
* **DISCOVER:** Parses all hosts on a subnet/CIDR (ie. 192.168.0.0/16) and initiates a sniper scan against each host. Useful for internal network scans.
|
||||
* **PORT:** Scans a specific port for vulnerabilities. Reporting is not currently available in this mode.
|
||||
* **FULLPORTONLY:** Performs a full detailed port scan and saves results to XML.
|
||||
* **MASSPORTSCAN:** Runs a "fullportonly" scan on mutiple targets specified via the "-f" switch.
|
||||
* **WEB:** Adds full automatic web application scans to the results (port 80/tcp & 443/tcp only). Ideal for web applications but may increase scan time significantly.
|
||||
* **MASSWEB:** Runs "web" mode scans on multiple targets specified via the "-f" switch.
|
||||
* **WEBPORTHTTP:** Launches a full HTTP web application scan against a specific host and port.
|
||||
* **WEBPORTHTTPS:** Launches a full HTTPS web application scan against a specific host and port.
|
||||
* **WEBSCAN:** Launches a full HTTP & HTTPS web application scan against via Burpsuite and Arachni.
|
||||
* **MASSWEBSCAN:** Runs "webscan" mode scans of multiple targets specified via the "-f" switch.
|
||||
* **VULNSCAN:** Launches a OpenVAS vulnerability scan.
|
||||
* **MASSVULNSCAN:** Launches a "vulnscan" mode scans on multiple targets specified via the "-f" switch.
|
||||
|
||||
- **NORMAL:** Performs basic scan of targets and open ports using both active and passive checks for optimal performance.
|
||||
|
||||
- **STEALTH:** Quickly enumerate single targets using mostly non-intrusive scans to avoid WAF/IPS blocking.
|
||||
- **FLYOVER:** Fast multi-threaded high level scans of multiple targets (useful for collecting high level data on many hosts quickly).
|
||||
- **AIRSTRIKE:** Quickly enumerates open ports/services on multiple hosts and performs basic fingerprinting. To use, specify the full location of the file which contains all hosts, IPs that need to be scanned and run ./sn1per /full/path/to/targets.txt airstrike to begin scanning.
|
||||
- **NUKE:** Launch full audit of multiple hosts specified in text file of choice. Usage example: ./sniper /pentest/loot/targets.txt nuke.
|
||||
- **DISCOVER:** Parses all hosts on a subnet/CIDR (ie. 192.168.0.0/16) and initiates a sniper scan against each host. Useful for internal network scans.
|
||||
- **PORT:** Scans a specific port for vulnerabilities. Reporting is not currently available in this mode.
|
||||
- **FULLPORTONLY:** Performs a full detailed port scan and saves results to XML.
|
||||
- **MASSPORTSCAN:** Runs a "fullportonly" scan on mutiple targets specified via the "-f" switch.
|
||||
- **WEB:** Adds full automatic web application scans to the results (port 80/tcp & 443/tcp only). Ideal for web applications but may increase scan time significantly.
|
||||
- **MASSWEB:** Runs "web" mode scans on multiple targets specified via the "-f" switch.
|
||||
- **WEBPORTHTTP:** Launches a full HTTP web application scan against a specific host and port.
|
||||
- **WEBPORTHTTPS:** Launches a full HTTPS web application scan against a specific host and port.
|
||||
- **WEBSCAN:** Launches a full HTTP & HTTPS web application scan against via Burpsuite and Arachni.
|
||||
- **MASSWEBSCAN:** Runs "webscan" mode scans of multiple targets specified via the "-f" switch.
|
||||
- **VULNSCAN:** Launches a OpenVAS vulnerability scan.
|
||||
- **MASSVULNSCAN:** Launches a "vulnscan" mode scans on multiple targets specified via the "-f" switch.
|
||||
|
||||
## Help Topics
|
||||
- [x] Plugins & Tools (https://github.com/1N3/Sn1per/wiki/Plugins-&-Tools)
|
||||
- [x] Scheduled scans (https://github.com/1N3/Sn1per/wiki/Scheduled-Scans)
|
||||
- [x] Sn1per Configuration Options (https://github.com/1N3/Sn1per/wiki/Sn1per-Configuration-Options)
|
||||
- [x] Sn1per Configuration Templates (https://github.com/1N3/Sn1per/wiki/Sn1per-Configuration-Templates)
|
||||
- [x] Sc0pe Templates (https://github.com/1N3/Sn1per/wiki/Sc0pe-Templates)
|
||||
|
||||
- [x] Plugins & Tools (<https://github.com/1N3/Sn1per/wiki/Plugins-&-Tools>)
|
||||
- [x] Scheduled scans (<https://github.com/1N3/Sn1per/wiki/Scheduled-Scans>)
|
||||
- [x] Sn1per Configuration Options (<https://github.com/1N3/Sn1per/wiki/Sn1per-Configuration-Options>)
|
||||
- [x] Sn1per Configuration Templates (<https://github.com/1N3/Sn1per/wiki/Sn1per-Configuration-Templates>)
|
||||
- [x] Sc0pe Templates (<https://github.com/1N3/Sn1per/wiki/Sc0pe-Templates>)
|
||||
|
||||
## Integration Guides
|
||||
- [x] Github API integration (https://github.com/1N3/Sn1per/wiki/Github-API-Integration)
|
||||
- [x] Burpsuite Professional 2.x integration (https://github.com/1N3/Sn1per/wiki/Burpsuite-Professional-2.x-Integration)
|
||||
- [x] OWASP ZAP integration (https://github.com/1N3/Sn1per/wiki/OWASP-ZAP-Integration)
|
||||
- [x] Shodan API integration (https://github.com/1N3/Sn1per/wiki/Shodan-Integration)
|
||||
- [x] Censys API integration (https://github.com/1N3/Sn1per/wiki/Censys-API-Integration)
|
||||
- [x] Hunter.io API integration (https://github.com/1N3/Sn1per/wiki/Hunter.io-API-Integration)
|
||||
- [x] Metasploit integration (https://github.com/1N3/Sn1per/wiki/Metasploit-Integration)
|
||||
- [x] Nessus integration (https://github.com/1N3/Sn1per/wiki/Nessus-Integration)
|
||||
- [x] OpenVAS API integration (https://github.com/1N3/Sn1per/wiki/OpenVAS-Integration)
|
||||
- [x] GVM 21.x integration (https://github.com/1N3/Sn1per/wiki/GVM-21.x-Integration)
|
||||
- [x] Slack API integration (https://github.com/1N3/Sn1per/wiki/Slack-API-Integration)
|
||||
- [x] WPScan API integration (https://github.com/1N3/Sn1per/wiki/WPScan-API-Integration)
|
||||
|
||||
- [x] Github API integration (<https://github.com/1N3/Sn1per/wiki/Github-API-Integration>)
|
||||
- [x] Burpsuite Professional 2.x integration (<https://github.com/1N3/Sn1per/wiki/Burpsuite-Professional-2.x-Integration>)
|
||||
- [x] OWASP ZAP integration (<https://github.com/1N3/Sn1per/wiki/OWASP-ZAP-Integration>)
|
||||
- [x] Shodan API integration (<https://github.com/1N3/Sn1per/wiki/Shodan-Integration>)
|
||||
- [x] Censys API integration (<https://github.com/1N3/Sn1per/wiki/Censys-API-Integration>)
|
||||
- [x] Hunter.io API integration (<https://github.com/1N3/Sn1per/wiki/Hunter.io-API-Integration>)
|
||||
- [x] Metasploit integration (<https://github.com/1N3/Sn1per/wiki/Metasploit-Integration>)
|
||||
- [x] Nessus integration (<https://github.com/1N3/Sn1per/wiki/Nessus-Integration>)
|
||||
- [x] OpenVAS API integration (<https://github.com/1N3/Sn1per/wiki/OpenVAS-Integration>)
|
||||
- [x] GVM 21.x integration (<https://github.com/1N3/Sn1per/wiki/GVM-21.x-Integration>)
|
||||
- [x] Slack API integration (<https://github.com/1N3/Sn1per/wiki/Slack-API-Integration>)
|
||||
- [x] WPScan API integration (<https://github.com/1N3/Sn1per/wiki/WPScan-API-Integration>)
|
||||
|
||||
## License & Legal Agreement
|
||||
For license and legal information, refer to the LICENSE.md (https://github.com/1N3/Sn1per/blob/master/LICENSE.md) file in this repository.
|
||||
|
||||
For license and legal information, refer to the LICENSE.md (<https://github.com/1N3/Sn1per/blob/master/LICENSE.md>) file in this repository.
|
||||
|
||||
## Purchase Sn1per Professional
|
||||
To obtain a Sn1per Professional license, go to https://sn1persecurity.com.
|
||||
|
||||
To obtain a Sn1per Professional license, go to <https://sn1persecurity.com>.
|
||||
|
||||
External attack surface management, Attack surface monitoring, Attack Surface Management Platform, Attack Surface Management Solutions, Vulnerability management, Threat intelligence, Cybersecurity risk assessment, Security posture assessment, Digital footprint analysis, Attack surface mapping, Web application security, Network security, Infrastructure security, Cloud security, Third-party risk management, Incident response, Penetration testing, Asset discovery, Patch management, Security scanning, Firewall configuration, Intrusion detection system, Security awareness training, Data breach prevention, Web server security, Endpoint security, Phishing protection, Vulnerability assessment, Network security, Web application testing, Ethical hacking, Security assessment, Information security, Red teaming, Cybersecurity testing, Pen testing tools, Exploitation techniques, Wireless network testing, Social engineering, Security auditing, Incident response, Intrusion detection, Firewall testing, Security assessment methodology, Risk assessment, Security controls, Web vulnerability scanning, Password cracking, Security testing services, Security architecture, System hardening, Network reconnaissance, Red teaming, Penetration testing, Cybersecurity, Vulnerability assessment, Attack simulation, Threat intelligence, Risk assessment, Security testing, Adversarial tactics, Incident response, Security assessment, Network security, Defensive measures, Security controls, Social engineering, Exploitation techniques, Security awareness, Defensive strategies, Risk mitigation, Blue teaming, Security operations, Intrusion detection, Security frameworks, Cyber defense, Information security
|
||||
|
||||
14
docker-compose-blackarch.yml
Normal file
14
docker-compose-blackarch.yml
Normal file
@@ -0,0 +1,14 @@
|
||||
version: '3.9'
|
||||
|
||||
x-logging: &default-logging
|
||||
options:
|
||||
max-size: "40m"
|
||||
max-file: "10"
|
||||
driver: json-file
|
||||
|
||||
services:
|
||||
blackarch:
|
||||
container_name: blackarch
|
||||
build:
|
||||
context: .
|
||||
dockerfile: Dockerfile.blackarch
|
||||
@@ -12,8 +12,3 @@ services:
|
||||
build:
|
||||
context: .
|
||||
dockerfile: Dockerfile
|
||||
blackarch:
|
||||
container_name: blackarch
|
||||
build:
|
||||
context: .
|
||||
dockerfile: Dockerfile.blackarch
|
||||
Reference in New Issue
Block a user